- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Printer Friendly Page
Yes. It is Possible to Make Security Operations Teams Happy and Effective.
Challenges faced by security teams:
Today, customers use hundreds of security products to protect their network from evolving threats right from applications, cloud infrastructure, to internal networks. But a big problem is that these products create silos and don’t communicate with each other either process point of view or data point of view, which makes it difficult for network admins to get real-time visibility into threats in an easy to consume manner. Also, these security products produce a large volume of incidents but security teams have difficulty in prioritizing the threats. Based on the Enterprise security group (ESG)-research-insight-report published in March 2017, security teams are constantly struggling to keep up with the volume of security alerts. These security teams are often understaffed and lack advanced skills necessary for security operations. These factors limit security operations effectiveness and make organizations extremely vulnerable to targeted attacks by sophisticated cyber-adversaries.
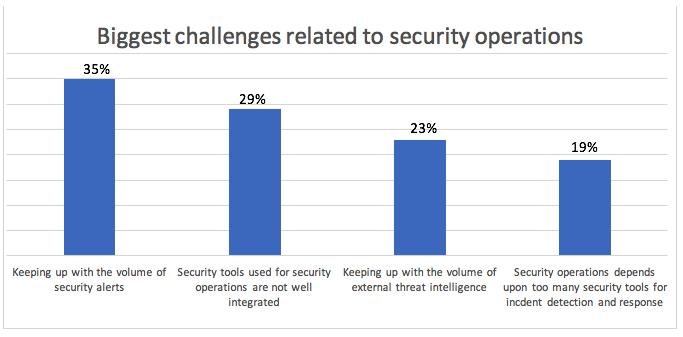
According to the survey conducted for the report cited above:
- Keeping up with the volume of security alerts (35%) and lack of integration between security tools used (29%) are the top two challenges related to security operations.
- Other major challenges include keeping up with the volume of external threat intelligence (23%) and dependency on too many security tools for incident detection and response (19%).
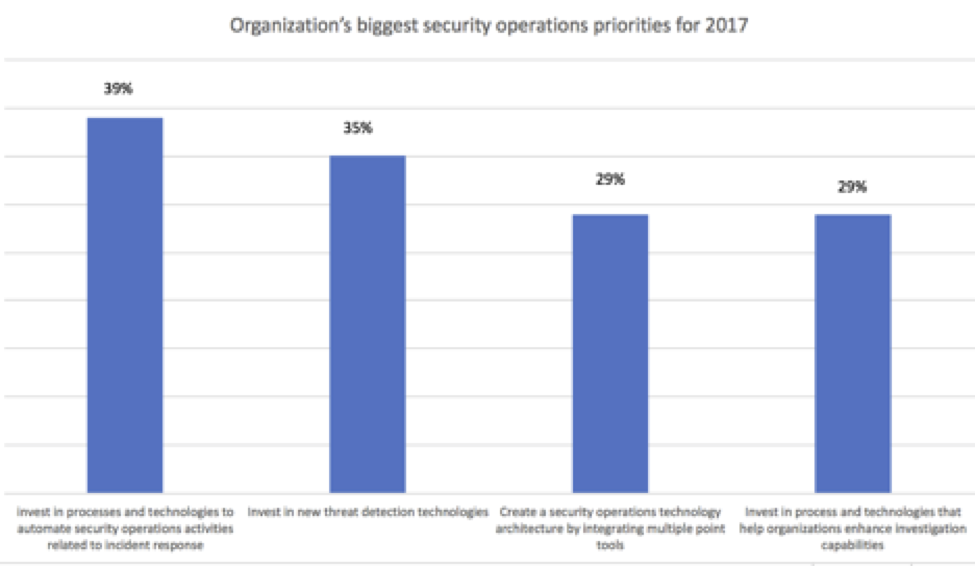
According to same ESG report, the top security operations priorities for 2017 include:
- Invest in technologies to automate security operations related to incident response (39%).
- Invest in new threat detection technologies (35%).
- Create a security operation architecture by integrating multiple tools (29%).
- Invest in process and technologies that help organizations enhance investigation capabilities (29%)
The figure below accurately depicts the GAP between where security teams are and associated issue with the current situation:
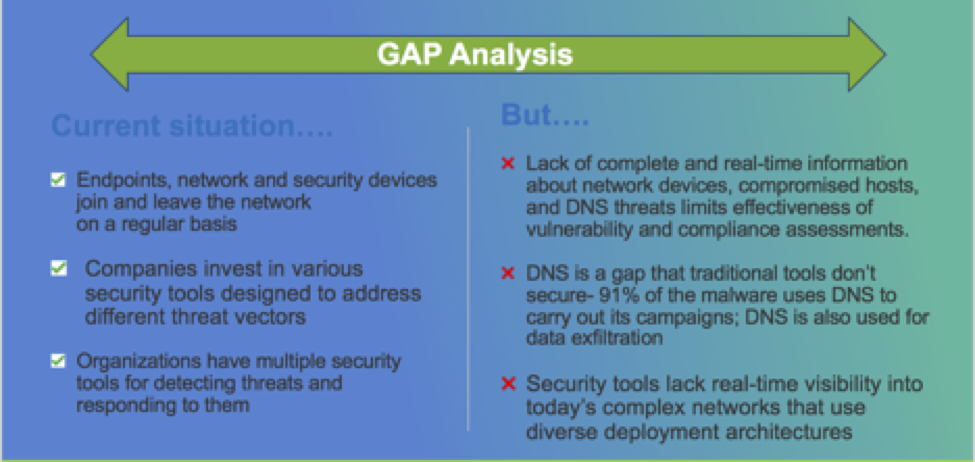
The Infoblox and Tenable SecurityCenter integration helps security team to bridge the gaps mentioned above.
Why Infoblox partners with Tenable: Tenable is world’s first Cyber Exposure platform that provides live discovery and visibility of all modern assets across the environment, add the context of risk to prioritize remediation and provides a clear view of your security posture.
Infoblox - Tenable Joint Solution Overview
The Tenable joint solution helps team alleviate these challenges by breaking down the silos and provides benefits such as context-based action, security orchestration, and improved security efficiency as shown in the figure below:
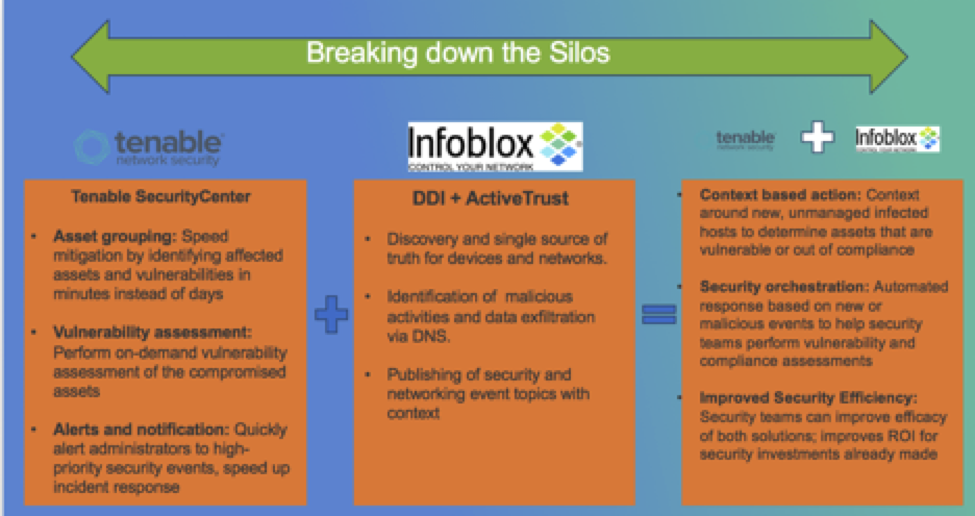
Infoblox is the first and only DDI vendor to integrate with Tenable to automate asset discovery, provide in-depth and continuous visibility and enhance overall security posture. This integration enables security operation teams to:
- Discover new assets automatically by searching the network, monitoring the traffic and gathering all information on network, hardware and web applications on the network.
- Gain visibility and context around new devices or hosts that join the network.
- Initiate on-demand scanning in near real-time when threats are discovered.
This to decide the priority of threats by providing of the threats and it also provides near-real-time visibility into network devices by discovering new assets automatically.
Solution diagram:
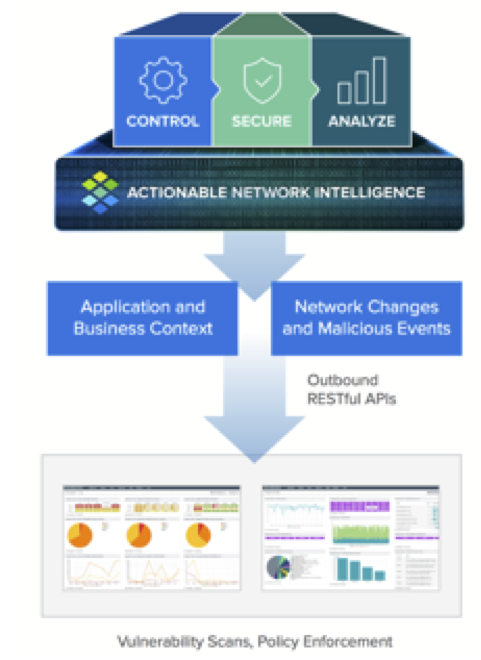
Benefits of the Infoblox-Tenable joint solution include:
- Security orchestration: By automating response to malicious events on the network, the integrated Infoblox-Tenable solution provides security orchestration by performing vulnerability and compliance assessment based on events in real time, thus eliminating blind spots within the network.
- The context for prioritization of threats: By leveraging DDI data, security teams can get context around unmanaged devices, infected hosts, which helps security teams prioritize action based on the actual risk of the asset.
- Improved ROI of security investments already made: Security teams can improve ROI for security investments already made by allowing different security tools to work together.
To summarize, Infoblox and Tenable joint solution enables automated response for network and malicious events, provide context to prioritize actions and allows 100s of security devices to work together, thereby reducing the volume of security alerts and saving invaluable time for network and security teams.
To learn more about the joint solution, read the solution note:
https://community.infoblox.com/t5/Tenable/Joint-Solution-Brief-Infoblox-and-Tenable/gpm-p/11126
Resources:
https://www.siemplify.co/resources/2017-esg-research-report-security-operations-challenges/
