Top Security Report #1: DNS Top RPZ Hits
This blog discusses the report #1 in a series of seven top security reports that can help you defend against bad actors.
Here are the previous parts: part 1, part 2, part 3, part 4, part 5, part 6, part 7
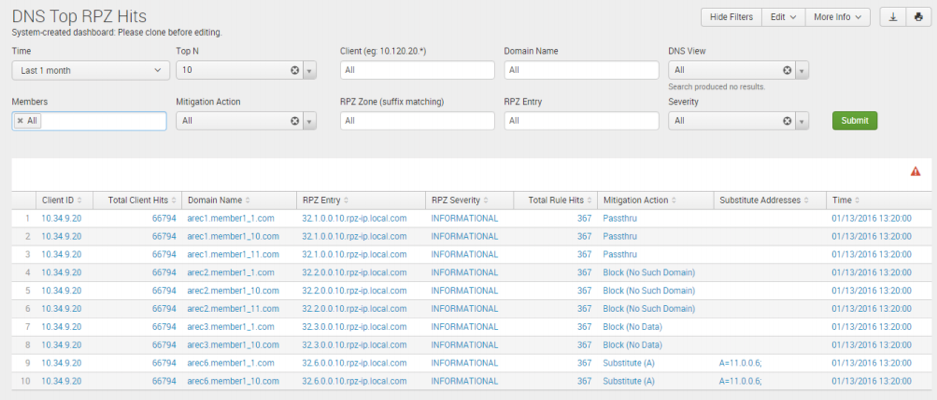
DNS Top RPZ Hits
Similar to top report #2, the DNS Top RPZ Hits report helps deliver data protection and malware mitigation by showing which clients have the most malicious activities using threat intel RPZ rules defined through Active Trust. Network admins need to know which clients are conducting bad DNS network queries, for monitoring and pre-emptive action. Security admins need to identify malicious real-time and historical clients and domains to cut response time for damage mitigation and resolution. A typical security use case occurs when a security admin needs to identify all the clients that are visiting a known malicious domain or all malicious domains a known infected client is engaging.
|
Top Report #1: DNS Top RPZ Hits |
|
|
Service Area |
Data Protection & Malware Mitigation |
|
Purpose |
Shows clients with the most malicious activities |
|
Primary User |
Network & Security Admins |
|
Importance |
Identifies RPZ domains which have the most hits from qualified malicious domains and shortens the time to identify malware impacts by tracking attempts made to reach domains on the RPZ list |
|
Use Case |
Enables security admins to identify all clients visiting a known malicious domain or all malicious domains a known infected client is engaging |
|
Available |
Out-of-the-box & requires Active Trust/Active Trust Cloud (AT/ATC) |
This report is located through the security dashboard and utilizes Active Trust/Active Trust Cloud. Admins can search and sort by time, top Number, client IP, domain name, DNS view, members, mitigation action, RPZ zone, RPZ entry, severity and detailed aggregated hits count. Admins can filter by severity level (all, critical, major, warning and informational) to quickly parse the domains that are of critical or major levels of concern, so they can run a virus scan or send it for further action by the security team. It can also be saved to run automatically at regular intervals, and if rules are violated, it can be programmed to trigger an alert, transfer a raw data file for further processing, run a script, send an SNMP trap to a security system, send an email to the security team, pass the alert to the syslog or other actions. This report can be used to share data with the security ecosystem and other tools on the network, to help identify and stop threats in their tracks.
Here are the seven (7) security reports that can give you an edge over the bad actors.
- Top Security Report #7: DNS Top NXDOMAIN – NOERROR
- Top Report #6: Threat Protection - Top Rules by Source
- Top Report #5: Top Malware & DNS Tunneling by Client
- Top Report #4: Tunneling Traffic by Category
- Top Report #3: DNS Top Tunneling Activity
- Top Report #2: Malicious Activity by Client
- Top Report #1: DNS Top RPZ Hits
Learn more:
- Join the Infoblox Reporting & Analytics Technical Demo Series to continue the discussion in the free webinar on 7/17, 2018, 9A PDT, 12P EDT, 5P BST. Register
- As an existing Infoblox DDI customer, you can deploy a virtual Infoblox Reporting & Analytics appliance free of charge — no strings attached. Download and try the Reporting & Analytics Free Tier today.
Categories
- All Categories
- 5.2K Forums
- 3.5K Critical Network Services
- 468 Security
- 1.2K Asset Visibility
- Ideas Portal
- Webinars & Events
- 291 Resources
- 291 News & Announcements
- Knowledge Base
- Infoblox Documentation Portal
- Infoblox Blog
- Support Portal
- 8 Members Hub
- 4 Getting Started with Community
- 4 Community Support
