- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Printer Friendly Page
Cyber Threat Advisory: HIDDEN COBRA: ELECTRICFISH
[ Edited ]- Mark as New
- Bookmark
- Subscribe
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
05-09-2019 12:38 PM - edited 05-09-2019 12:57 PM
Title: Cyber Threat Advisory: HIDDEN COBRA: ELECTRICFISH
Date: 9 May 2019
Author: Christopher Kim
TLP: WHITE
- Executive Summary
On 9 May, the Department of Homeland Security (DHS) and Federal Bureau of Investigation (FBI) jointly published a Malware Analysis Report (MAR) about a trojan malware variant known as ELECTRICFISH.1 DHS and the FBI report that it is being used by the North Korean government, and categorizes malicious activity by this actor as HIDDEN COBRA.2
The MAR described ELECTRICFISH malware as a 32-bit Windows executable file, and recommended response actions and mitigation techniques. The targets of interest for ELECTRICFISH are unknown, but HIDDEN COBRA3 activity has historically been focused against the media, aerospace, and financial industries, as well as other critical infrastructure industries.
The following advisories from the Infoblox Cyber Intelligence Unit provide additional information and context about past HIDDEN COBRA activity:
- HIDDEN COBRA: HOPLIGHT (Apr 2019)3
- HIDDEN COBRA: FASTCash (Oct 2018)4
- HIDDEN COBRA: Keymarble (Aug 2018)5
- HIDDEN COBRA: Typeframe (June 2018)6
- HIDDEN COBRA: Brambul Worm & Joanap RAT (May 2018)7
- HIDDEN COBRA: Fallchill RAT & Volgmer Trojan (November 2017)8
- Analysis
ELECTRICFISH is a 32-bit Windows executable application and command-line utility that funnels network traffic between an infected client and the actor's server. The application first establishes a Transmission Control Protocol (TCP) session between the client and server and then uses a custom protocol to exchange data.
ELECTRICFISH is also equipped with extra features to work with a proxy server that intercepts requests between client and server without proper authentication. The malware can be configured with a proxy username and password that allows the actor to authenticate the client sitting behind a proxy server, and to communicate with a server outside the target's network.
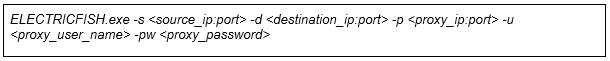
The application accepts several command-line arguments including the following:
- destination IP address and port (C2 server)
- source IP address and port (infected client)
- proxy IP address and port (proxy server)
- username / password (proxy server)
The above arguments can be used in combination to establish the communication channel between client and server. An example of a command with ELECTRICFISH is provided below:
- Prevention and Mitigation
The Cybersecurity and Infrastructure Security Agency (CISA) recommends the following mitigation techniques to defend against attacks that use malware similar to ELECTRICFISH. CISA also stresses that it is crucial to review system configuration changes with system owners and administrators before implementing them because users may face unwanted impacts that can damage their business.
- Maintain up-to-date antivirus signatures and engines.
- Keep operating system patches up-to-date.
- Disable file and printer sharing services. If these services are required, use strong passwords or Active Directory authentication.
- Restrict users’ ability (permissions) to install and run unwanted software applications. Do not add users to the local administrators group unless required.
- Enforce a strong password policy and implement regular password changes.
- Exercise caution when opening email attachments, even if the attachment is expected and the sender appears to be known.
- Enable a personal firewall on agency workstations, configured to deny unsolicited connection requests.
- Disable unnecessary services on agency workstations and servers.
- Scan for and remove suspicious email attachments; ensure the scanned attachment is its “true file type” (i.e., the extension matches the file header).
- Monitor users’ web browsing habits; restrict access to sites with unfavorable content.
- Exercise caution when using removable media (USB thumb drives, external drives, CDs, etc.).
- Scan all software downloaded from the internet prior to executing.
- Maintain situation awareness of the latest threats and implement appropriate Access Control Lists (ACLs).
- Indicators of Compromise (IOCs)
|
Indicator |
Description |
|
a1260fd3e9221d1bc5b9ece6e7a5a98669c79e124453f2ac58625085759ed3bb |
PE32 MS Windows SHA256 |
|
header: 08bb17d8e839e7fc92426e813a696e73 .text: 6c3daca3c522ab98a8ac12a45087297c .rdata: 3d3d7962d16652002018640a3fa27d44 .data: b7f382ea7e6c9c8e737cb92551341e64 .rsrc: 871fb8486e5ea3307ff7b65ddf46518a .reloc: 382715f8e776a544bf70f843a52e3ff2 |
PE sections MD5 |
|
lsass.exe a1260fd3e9221d1bc5b9ece6e7a5a98669c79e124453f2ac58625085759ed3bb.exe |
Process list |
Endnotes
- https://www.us-cert.gov/ncas/analysis-reports/AR19-129A
- https://www.us-cert.gov/HIDDEN-COBRA-North-Korean-Malicious-Cyber-Activity
- https://sites.google.com/a/infoblox.com/cyberint-threat-labs/home/publication-repo/20190410_HIDDEN_C... CTA_Endnotes.pdf
- https://sites.google.com/a/infoblox.com/cyberint-threat-labs/home/publication-repo/20181006_HIDDEN_C... CTA_Endnotes.pdf?attredirects=0&d=1
- https://sites.google.com/a/infoblox.com/cyberint-threat-labs/home/publication-repo/20180809_CTA_KEYM... Endnotes.pdf?attredirects=0&d=1
- https://sites.google.com/a/infoblox.com/cyberint-threat-labs/home/publication-repo/20180618_CTA_Type... 20%282%29.pdf?attredirects=0&d=1
- https://sites.google.com/a/infoblox.com/cyberint-threat-labs/home/publication-repo/CTA-2018-001%20Br... 20Worm%20%26%20Joanap%20RAT%20%282%29.pdf?attredirects=0&d=1
- https://sites.google.com/a/infoblox.com/cyberint-threat-labs/home/publication-repo/CTA-2017-004_Hidd.... pdf?attredirects=0&d=1