- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Printer Friendly Page
NetMRI policy rule to monitor for IPs configured outside of defined subnet
- Mark as New
- Bookmark
- Subscribe
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
04-24-2019 08:54 PM
Hey all,
Is there a way to create a custom NetMRI policy rule that will check for any rogue IP address in a configuration that is outside of a defined subnet? If so, what do you think the most efficient method is?
Cheers,
Rich
Re: NetMRI policy rule to monitor for IPs configured outside of defined subnet
- Mark as New
- Bookmark
- Subscribe
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
04-25-2019 05:48 AM
Can you post an example of each? It will help us see what you are trying to achive
Twitter: https://twitter.com/sifbaksh
https://sifbaksh.com
Re: NetMRI policy rule to monitor for IPs configured outside of defined subnet
- Mark as New
- Bookmark
- Subscribe
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
04-27-2019 01:01 PM
I have switch configurations with various IP addresses referenced throughout (i.e. virtual interfaces, ntp servers, snmp server, dns name servers, default gateway, etc.). All those IP addresses in my configs reside in a couple different subnets (i.e. 10.80.10.0/24, 10.80.11.0/24).
Let's say a bad actor logged onto a switch and configured an interface and snmp-server in 192.168.1.0/24, outside of those two subnets above. I want to write a policy in NetMRI that would alert on that "untrusted subnet" configuration change. In other words, any configured IPs within those two subnets above would be "safe", anything deviating from those I would want to know about.
I'm struggling with how to write the policy and am looking for some guidance.
Re: NetMRI policy rule to monitor for IPs configured outside of defined subnet
- Mark as New
- Bookmark
- Subscribe
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
04-29-2019 07:26 AM
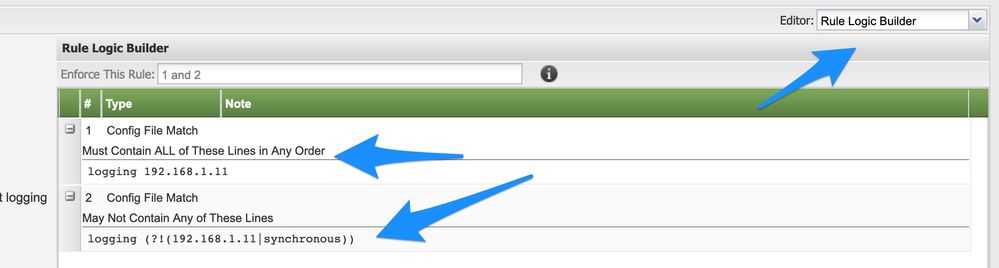
Well I would approach it a diffrent way using Rule Logic Builder and Negative Look Ahead in RegEX
What the above mean is that if any other logging server besides 192.168.1.11 this will through an error
So now you can do that that for Logging, TACACS Servers, SNMP, etc...
I hope this helps
Twitter: https://twitter.com/sifbaksh
https://sifbaksh.com
Re: NetMRI policy rule to monitor for IPs configured outside of defined subnet
- Mark as New
- Bookmark
- Subscribe
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
05-01-2019 09:07 AM
Sif,
Good tip on the negative lookahead. Is that how the CPD is implemented when one has:
required:
access-list 123 permit ip 1.1.1.1
invalid:
access-list 123 .*
Re: NetMRI policy rule to monitor for IPs configured outside of defined subnet
- Mark as New
- Bookmark
- Subscribe
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
05-01-2019 10:40 AM
I will have to double check CPD, I haven't used it in like 7 years
Twitter: https://twitter.com/sifbaksh
https://sifbaksh.com
Re: NetMRI policy rule to monitor for IPs configured outside of defined subnet
- Mark as New
- Bookmark
- Subscribe
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
05-01-2019 11:02 AM
Of course you know I had to test it ![]()
And yes you are correct CPD does worked that way
Twitter: https://twitter.com/sifbaksh
https://sifbaksh.com
Re: NetMRI policy rule to monitor for IPs configured outside of defined subnet
- Mark as New
- Bookmark
- Subscribe
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
05-01-2019 01:59 PM
I know that CPD has been deprecated but it's so intuitive for "mortals" who want to copy/paste config snippets. And it has always accepted regex if one used that.
Re: NetMRI policy rule to monitor for IPs configured outside of defined subnet
[ Edited ]- Mark as New
- Bookmark
- Subscribe
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
06-04-2019 09:16 PM - edited 06-04-2019 09:34 PM
Sbaksh,
Thank you for the information here; this seems to work!
One issue now though is that the rules only pick up the *first* violation in the configuration. The second violations (and beyond) seem to be ignored in my tests. Is there a way to find and report on *all* violations instead of just the first one within Rule Logic Builder?
My final related question is that I am trying to build the rule checks against *custom* fields I have set on some devices. I only see a fixed list of default attributes to choose from. Am I missing something or am I just stuck with the default attributes here?
Thanks again,
Rich
Re: NetMRI policy rule to monitor for IPs configured outside of defined subnet
- Mark as New
- Bookmark
- Subscribe
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
06-05-2019 07:30 AM
Can you post your rule?
Either a screenshot or upload the XML
Twitter: https://twitter.com/sifbaksh
https://sifbaksh.com